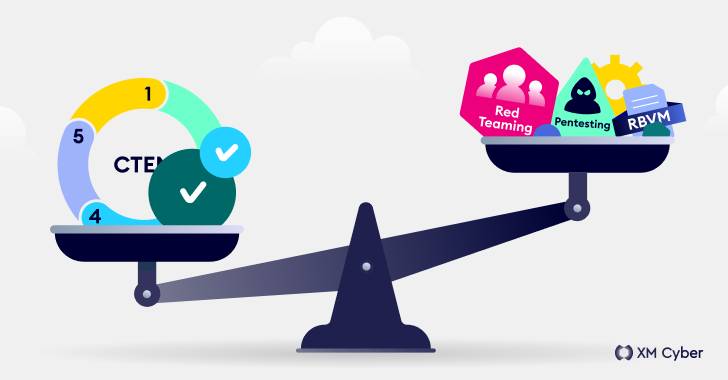
How Attackers Can Own a Business Without Touching the Endpoint
Attackers are increasingly making use of “networkless” attack techniques targeting cloud apps and identities. Here’s how attackers can (and are) compromising organizations – without ever needing to touch the endpoint or conventional networked systems and services. Before getting into the details of the attack techniques being used, let’s discuss why

What's Your Reaction?























































![Watch: The Butterfly Circus [Short Film] featuring Nick Vujicic](https://blog.elfglobal.org/uploads/images/202405/image_430x256_6654b9bc69c46.jpg)









![Watch: The Butterfly Circus [Short Film] featuring Nick Vujicic](https://blog.elfglobal.org/uploads/images/202405/image_140x98_6654b9bc76b8e.jpg)




